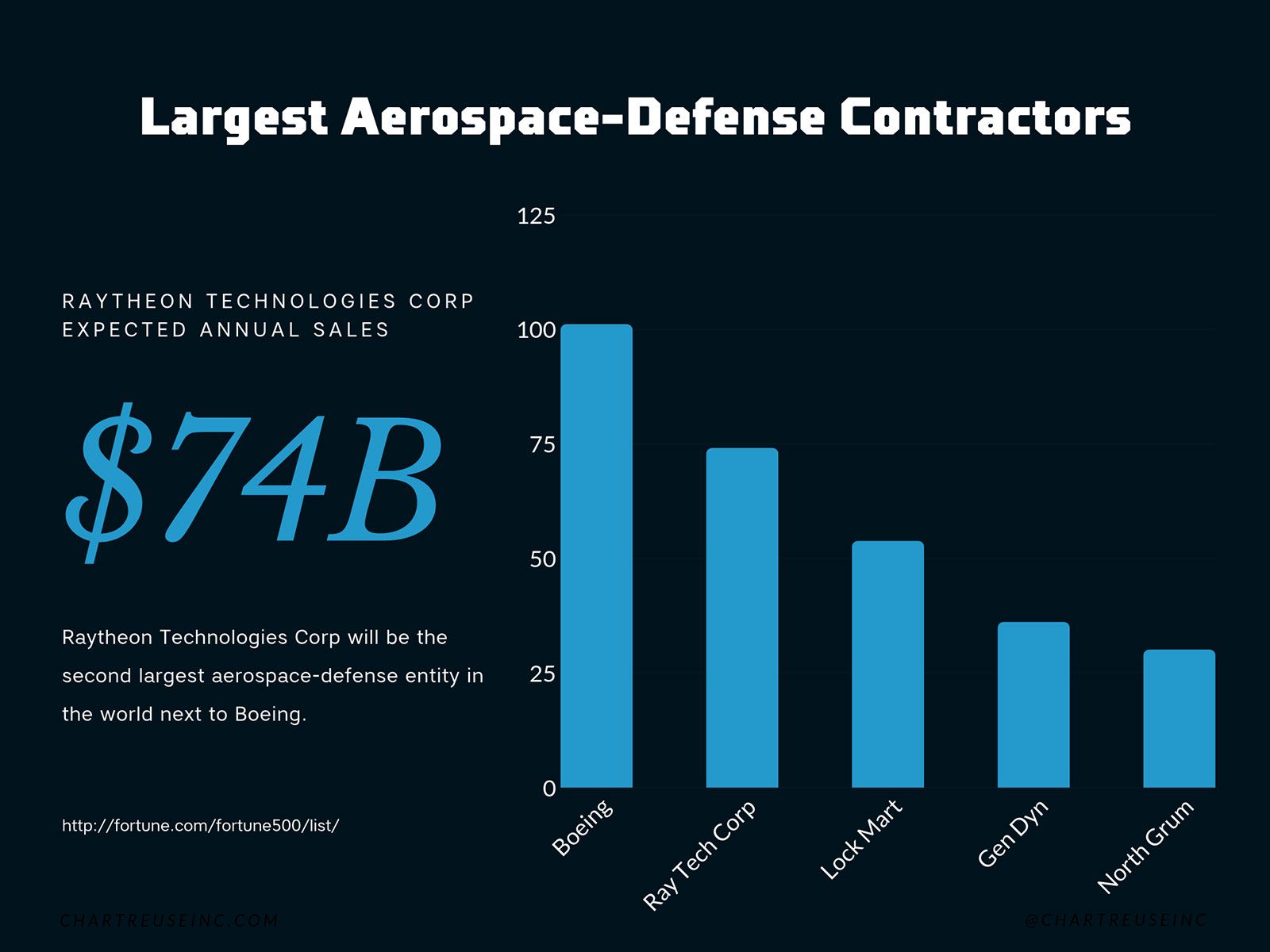
Last month, aerospace giant United Technologies and defense leader Raytheon announced their merger. The new company, Raytheon Technologies Corp, will be the second largest aerospace-defense entity in the world. And while most of the aerospace-defense world reacted with varying degrees of surprise, some are looking at this merger a bit more skeptically.
President Donald Trump, particularly, raised some very specific concerns about the unification.
In an interview with CNBC, Trump expressed his apprehension toward the deal. Basically, he’s worried it might hurt competition in government contract dealing. If both companies make the same or similar products, their merger would cancel out competition and give the government one less entity to negotiate with and accept bids from.
And though it’s always fair to question decreased competition when considering mergers, that’s not the biggest problem with the United Technologies / Raytheon deal. While analysts discuss potential issues with pension payouts, job losses, and relocation logistics; the real issue surrounding this merger is the increased potential for successful cyber attacks that threaten national security.
The Threat
Of course both companies will engage in detailed cybersecurity due diligence before the merger is complete, but uncovering past breaches is only part of the cyber exposure in a union this size. The greater risk lies in newly generated weaknesses created during the merge.
When any two companies combine, they have to figure out how to integrate their networks and systems to work as one. The potential for oversights and interoperability increases exponentially – and as a byproduct, those integrations create security gaps, leaving opportunities for immediate and eventual privacy and security issues.
Considering no company has perfect security on its own, it’s hard to imagine a scenario where two giant companies integrate their individually flawed systems and don’t create a hacker haven.
Though neither Raytheon nor United Technologies has reported a breach since 2017, both companies have experienced security issues in the past.
Past Security Issues
Several years ago, hackers breached security systems of several defense contractors, including Raytheon. The hackers may have accessed sensitive data on weapons systems and other military technologies. Raytheon says it took immediate action once the hack was discovered, but didn’t publicize what information was stolen.
Around the same time, United Technology’s Sikorsky Aircraft (now part of Lockheed Martin) enabled a hack that likely exposed employee Social Security numbers, helicopter designs, and trade secrets. Critics argued United Technologies didn’t mention the breach in their SEC filings.
Most companies don’t broadcast their cybersecurity shortcomings – and in merger situations, those security flaws are less likely to remain covered and more likely to be exploited by hackers.
Think about it… it’s easier to infiltrate one quasi-integrated system than two separate systems. Cyber criminals know that. And if threat actors are looking to access current or future sensitive government information, the time to nest in the systems and networks of Raytheon Technologies Corp is during this merger.
Future Security Implications
Even after the merger is complete, the new company will have to implement a consistent security structure across the organization. All employees will need to get onboard with new procedures and protocols.
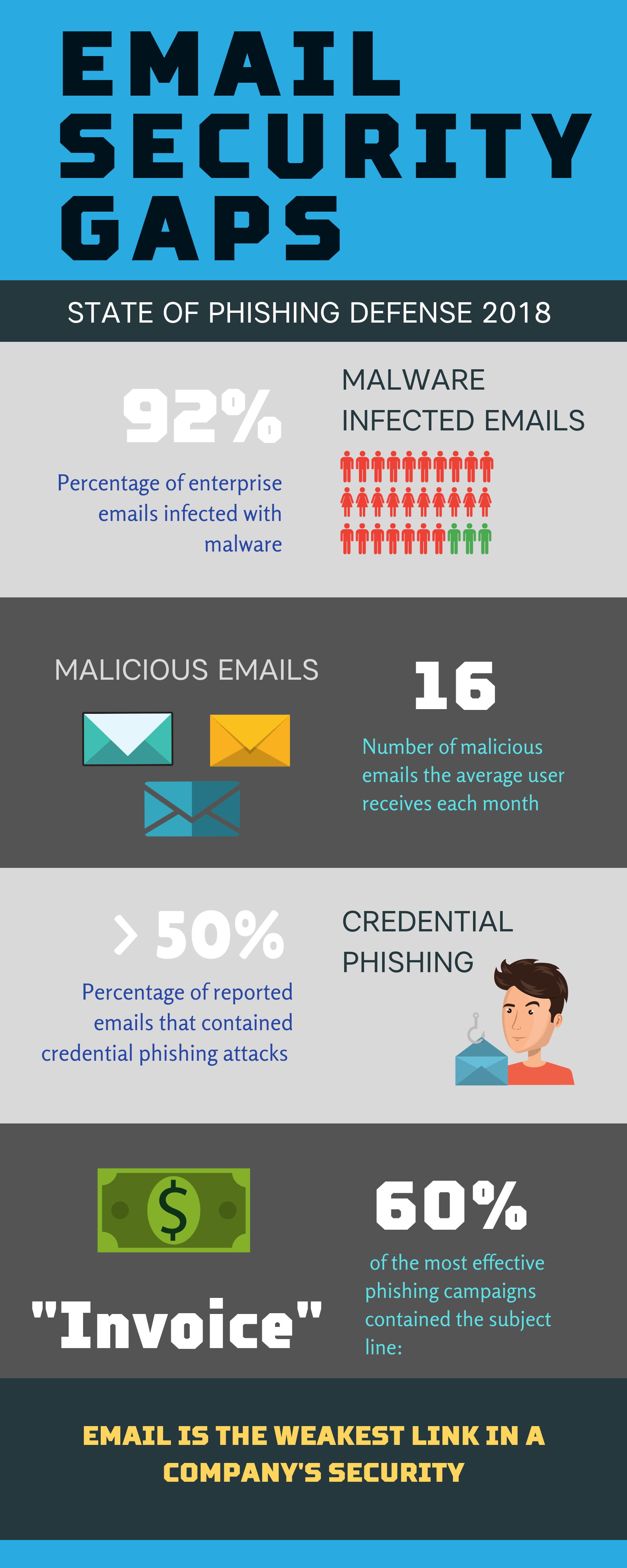
Those cybersecurity change management challenges alone will present numerous hacking opportunities. And considering that over 90% of data breaches start with an employee email, hackers could take advantage of any employee confusion or misalignment during the merger to execute successful phishing attacks.
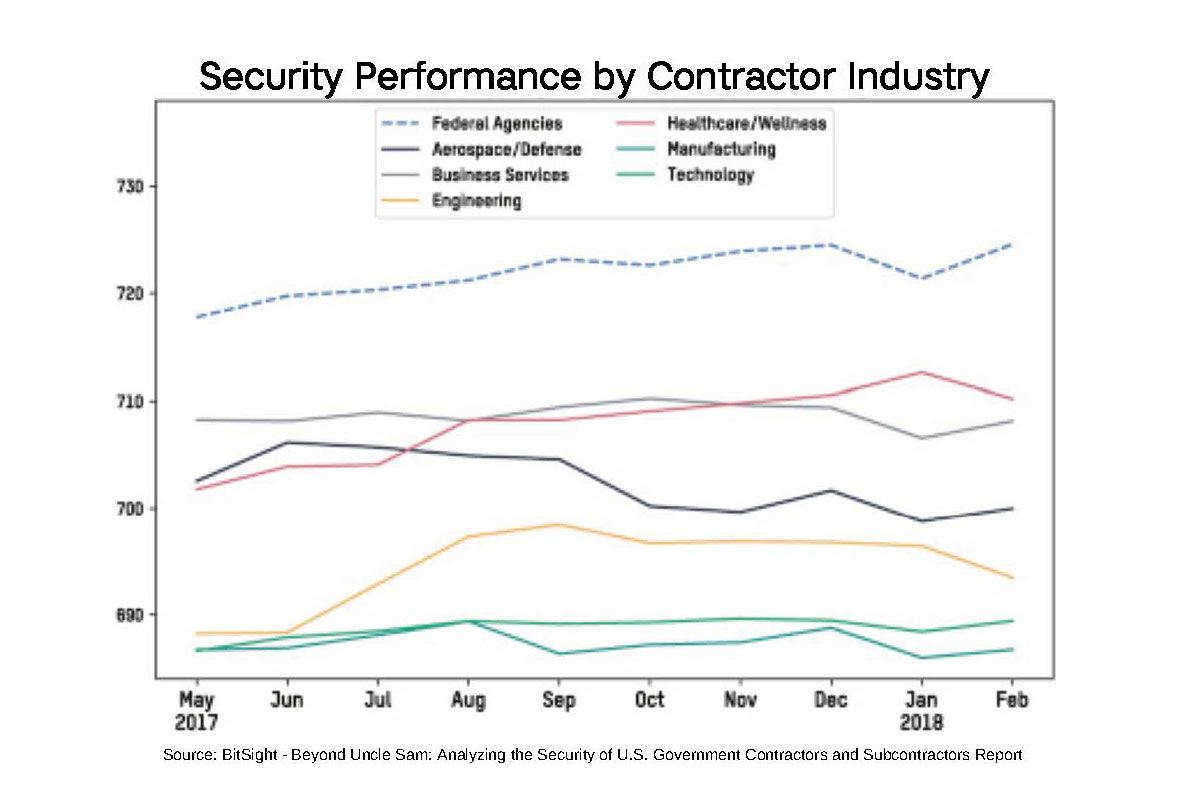
Though United Technologies and Raytheon face heightened and unique challenges because of their merger, they’re not alone in the problematic world of cyber issues and defense contractors.
In fact, cyber breaches and information insecurity are well-documented amongst America’s defense contractors and serve as hacker gateways to military and defense secrets.
America’s Defense Weakness
The United States has the highest funded military in the world – outspending other military powers, like China and Russia, by nearly 300%. In fact, the US spends more on military and defense than the next seven nations combined.
And that’s extremely significant when you talk about resources like manpower, equipment, and technology. On paper, the US reigns supreme in formidability – unstoppable in her defense and offense.
So why have national security experts recently cast doubts on the United States military’s seemingly obvious advantage?
The National Defense Strategy Commission concluded that “The security and well-being of the United States are at greater risk than at any time in decades,” and that “America’s military superiority has eroded to a dangerous degree.”
For nearly two decades, America’s defenses have been engaged from multiple fronts: fighting terrorism in the Middle East, navigating increasingly hostile relationships with nations that were previously considered quasi-allies, and defending against what is likely the most serious threat of all – cyberwar.
America’s defense resources are stretched increasingly thin as a result of these prolonged, growing threats, and budgeting restrictions haven’t helped.
To fill in necessary gaps, the government often looks to defense contractors with the capability of providing operational support.
For context, in 2017 the federal government committed about $507 billion in defense contracts.
Defense Contractors
Defense contractors are clearly a major player in America’s military strategy and their success lends to the success of the country.
So it’s troubling to note that a recent study found a significant number of defense contractors have reported a data breach since 2016.
We know that a single cyber breach can have crippling secondary and tertiary effects, but when the hacked entity houses national secrets and sensitive information about government and military personnel, top secret weapons programs, and defense system plans and strategies…
… those breaches put US national security in danger.
The study also discovered that nearly 50% of defense contractors follow subpar practices for network encryption and email security. Remember, the vast majority of breaches are caused by email attacks, so this vulnerability puts the federal government in grave danger.
As with individuals and non-government affiliated companies, it’s likely that cyber criminals will try to infiltrate defense contractors through phishing. But unlike in the civilian world, when a government vendor falls victim to a phishing scheme, it can lead to the exposure of critical defense information.
Breaches
Navy Contractor
One high profile example of how hackers use phishing attacks to breach defense contractors and gain access to the government happened just last year.
In 2018, Chinese government hackers infiltrated computers belonging to a Navy contractor via a phishing scheme.
The hackers accessed and stole a trove of highly sensitive information related to undersea warfare. This information included weapons plans, information about cryptographic systems, and signals data.
Experts believe China is working to develop systems that can disrupt the United States Navy’s defense capabilities. And when China can’t develop the right technologies, it steals data and plans from the US.
But how is China able to steal from the best funded defense structure in the world?
China’s government hackers have a thorough understanding of cyber crime. They recognize the intricacies of comms vulnerabilities. What’s more, they’re likely to set their sights on defense contractors as a weak link to access the federal government.
DoD Vendor
Cyber criminals aren’t only interested in weapons information. Last year, a defense contractor for the Department of Defense suffered a cyber breach that exposed the personal information and credit card data of US military members and civilian personnel.
As many as 30,000 people were affected.
Not only does a breach this size compromise those individuals’ financials, it could impact their safety.
In the wrong hands, personal and financial information can expose military members’ location, giving criminals enough information to physically target service members and their families.
And when sophisticated criminals have access to sensitive financial data, military members become more susceptible to extortion and bribery. Though many extortion cases involve blackmail for money, service members with knowledge of government secrets could be extorted for information.
Spear Phishing Scheme
In late 2018, security researchers reported that Russian hackers executed a spear phishing scheme targeting military agencies, law enforcement agencies, media companies, and defense contractors.
The hackers impersonated US State Department officials and contacted select individuals in order to gain access to targeted computer systems.
While larger defense contractors may have more strenuous phishing awareness programs, many smaller contractors with less resources don’t.
But size is generally not a barrier to entry when selecting contractors to access sensitive government information. And even if it was, large companies are not immune to phishing attacks.
Adding basic communications insecurities to other system vulnerabilities creates the perfect environment for cyber thieves.
Will a United Technologies / Raytheon communications breach be next?
The Way Forward
The United Technologies and Raytheon merger highlights the issues and severe implications around defense contractors and cybersecurity. The US government is aware of these dangers and is working to instill further compliance and oversight of cybersecurity in regard to contract acquisition.
But, even with regulatory measures, many defense contractors aren’t able to meet the requirements, and the government hasn’t been very strict in suspending noncompliant companies.
Strategists have suggested everything from imprisoning contractor leaders that enable breaches to offering a contracting incentive to companies that check certain risk mitigation blocks.
But the problem isn’t that defense contractors don’t care about protecting the nation’s secrets. They don’t intend for bad actors to attack their systems.
Is jail time a real answer?
On the other hand, should the government reward the biggest, richest contracting companies because they can afford the largest IT staff and newest cyber “solutions”? Should the Raytheon Technologies Corps of the contracting world get preferential treatment in all bids?
Surely, the answer is somewhere in the middle. Defense contractors and vendors need to prioritize cybersecurity and gain a real understanding of their risk landscape and exposures.
They need to budget accordingly for effective cybersecurity mitigations. And, they need to look at their own vendors and evaluate the cyber records of those vendors.
And what’s the best place to start?
… The basic communications layer.
Improving Basic Communications
Improving basic communications security is the most effective way to strengthen risk posture, and it doesn’t take an extensive IT department and significant investment in new cyber services to do it.
Because most breaches start with email, defense contractors of all sizes need to simply strengthen their communications security at this foundational level. After all, IT departments and expensive tools are useless when all hackers have to do is get the right person to open the wrong email.
We often overlook this fact, but the problem with email is that it’s inherently insecure. Even services that claim to provide secure email sources are riddled with vulnerabilities.
If defense contractors can curtail or eliminate their risks associated with email, they will significantly reduce their overall risk profile, strengthen their cybersecurity posture, and further safeguard America’s defense secrets.
Fortunately, HighSide provides a secure communications solution that serves as an alternative to email. This communications and work collaboration platform allows defense contractors to send and receive messages while completely eliminating risks associated with phishing and other email-based attack patterns.
With HighSide, defense contractors can store and share files securely, bypassing risks with shared service providers and cloud services.
Most security breaches are preventable with the right mitigation strategy, and that strategy must include an effective way to overcome basic communications-level risks.
The best way to do that is with HighSide.
The war of the future is a cyberwar. The groundwork is set – and even in today’s more traditional battles, cyber always seems to find a way in.
It’s time for defense contractors to embrace that they, too, are part of America’s cyber battles and have an obligation to help keep her military’s data and national secrets safe.
We’re looking to Raytheon Technologies Corp to lead the way.
 Cecilia Clark
Cecilia Clark