In Monty Python and the Holy Grail, Sir Lancelot charges guards at a castle’s gates, but abnormally. There is repeated footage of a distant charging Sir Lancelot alternated in with footage of the peaceful guards. Each time the camera cuts back to Sir Lancelot, he is charging from the same spot, never gaining ground. Then, suddenly, seemingly without ever having approached, Sir Lancelot jumps upon the hapless guards and kills one of them.
Unfortunately, entities subject to Cybersecurity Maturity Model Certification (CMMC) Compliance are the guards here, and Sir Lancelot is CMMC enforcement.
The skinny on CMMC
The United States Department of Defense (DoD) estimates that roughly $600 billion, or 1% of the global gross domestic product, is lost through cyber theft each year. The DoD created new Cybersecurity Compliance Requirements for contractors to reduce the theft of intellectual property. Their CMMC effort builds upon existing regulation (DFARS 252.204-7012) that is based on trust by adding a verification component with respect to cybersecurity requirements. The CMMC gives the DoD a mechanism to certify the cyber readiness and Maturity Level of defense contractors.
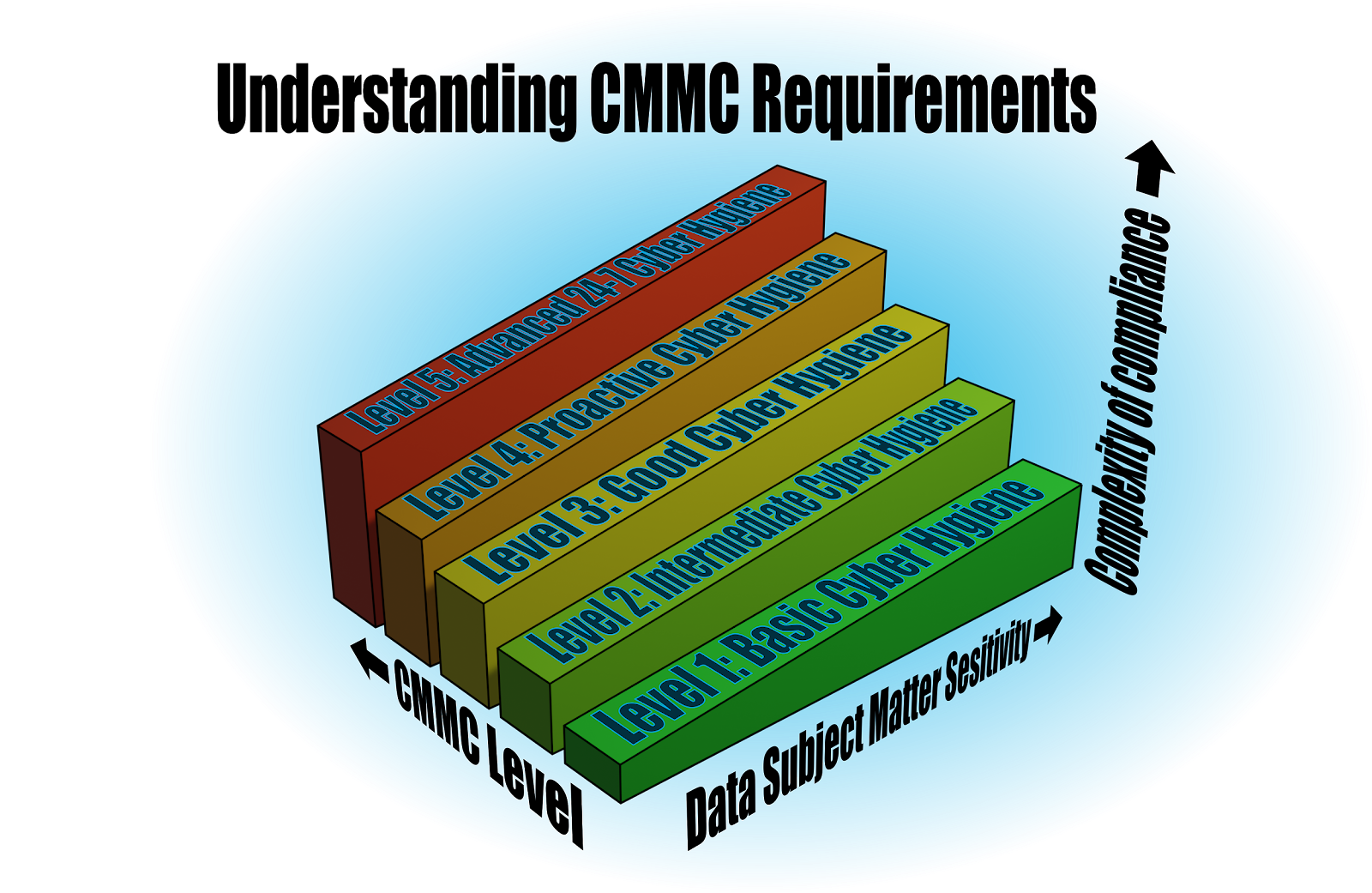
CMMC provides for five levels of certification in both cybersecurity practices and processes. Failure to adhere to these new requirements will result in loss of contracts with the DoD.
Unfortunately, and the reason for the comparison to the Monty Python sketch, there is still massive confusion surrounding the deadlines for CMMC certification. COVID-19 may or may not be at fault for this. Suffice it to say, what we do know is that all DoD suppliers will need CMMC certification by 2025 and that certification is valid for three years.
Getting ready for CMMC accreditation
While deadlines and delays get sorted out, the CMMC Accreditation Body does provide useful high-level information to getting prepared:
Path to CMMC-Accredited Body Certification in 10 steps:
- Understand CMMC Requirements
- Identify your scope. Enterprise, Organization Unit or Program Enclave
- Identify the desired Maturity level
- Optional. Pre-assess using an RPO or C3PAO
- Close any identified gaps
- Find a C3PAO on the CMMC-AB Marketplace
- Conduct the Assessment with C3PAO’s Certified Assessment Team
- Allowance of up to 90 days to resolve findings (if any)
- CMMC-AB reviews submitted assessment
- Upon approval, 3-year Certification issued!
They also give the useful advice of planning on at least six months for the certification process. This should not come as a surprise to those of you who are used to working with the government. But for those that are not, it might be a good idea to pad that expectancy further. The takeaway here is that passing CMMC assessment requires preparation. Whatever efforts organizations invest in the readiness on the front saves them double the effort on the back end
It’s all about People, Process & Technology
Successfully passing an CMMC assessment requires significant preparation. There are three areas when dealing with Controlled Unclassified Information (CUI) that require focus. These three key functional areas which impact CUI:
- People:
- How is your staff trained in the handling of CUI?
- What kinds of threats do your staff face from motivated adversaries interested in gaining unauthorized access to CUI?
- Have there been any accidental disclosures or inadvertent incidents involving CUI in the recent past among your staff and affiliated third parties?
- Processes:
- What processes exist to govern the creation, management and destruction of CUI?
- How are processes documented?
- What are the consequences of process violation?
- Are you currently evaluating active threats against the CUI projects which you are responsible for?
- Technology:
- How is your staff using technology to create and manage CUI?
- What controls are in place to assure that unauthorized individuals are not abusing their IT system privileges to gain access to CUI?
- What monitoring and response capabilities do you have in the event an incident is detected involving CUI?
- Plan on 17 to over 150 individual assessment criteria being evaluated depending on the level of certification.
Preparation for assessment should be done across:
- All team members with access to program documentation (in any format, including email and attachments)
- All IT staff with privileges that could be used to gain access to program documents/data
- All service providers with privileges that could be used to gain access to documents/data or systems.
- Pass-through work is assumed liability
- You will need an attestation from sub-contractors
- The goal should always be to REDUCE SCOPE.
- Reduce your scope by reducing your technology footprint. (HighSide helps here)
- It is nearly impossible to comply without significantly limiting WHO has access to WHAT information and WHERE they have access to the SYSTEMS that store and process program information.
- Reduce risk inherent to privileges
If that seems like a lot, a step back would be to start here:
- Number of people involved who touch data.
- Number of systems involved.
- Volume/type of data involved and how it is shared and stored.
Being able to answer those three questions is the minimum needed to get started, or to provide enough information to a third party to do any meaningful scoping for preparedness assistance. Accepting money from the government without being able to answer these three questions means it is time to change your organization’s SOPs in respect to working with the DoD.
CMMC resources, official and unofficial
Official information on the CMMC is available here. The most recent CMMC Model v1.02 . Being prepared for the time when CMMC finally makes it over the hill and to your castle’s gates will take planning and may take considerable time and effort. HighSide secure solutions help simplify the road to CMMC certification. Through HighSide’s secure collaboration platform, you can control who and where data can be shared from. Our MFA solution gives you the controls over who and where data is accessed, and HighSide’s encrypted file sharing platform provides you with a secure means to store and collaborate on projects. In a nutshell, once you can answer the big three questions in preparation of CMMC certification, our solution provide the teeth to do something with that information.
Download the HighSide CMMC compliance brief here
Doing nothing in the hopes that these requirements will continue to be pushed down the road is not a successful long-term plan. Determine your required cyber readiness maturity level and work from there. Don’t be caught at the gates because of present delays. Hit us up on chat, or email us at info@highside.io for further assistance.
 Evan Blair
Evan Blair